24 April 2020
Malicious campaigns against Azerbaijan’s government and industrial organizations
Cisco Talos experts have uncovered malicious campaigns involving a previously unknown remote-access Trojan (RAT), which has been dubbed PoetRAT. According to the researchers, the attacks targeted Azerbaijan’s government sector and industrial companies, mainly those in the energy sector. It was established during the investigation that the attackers were interested in SCADA systems related to wind turbines.
PoetRAT has a feature set that is standard for this type of malware. It allows the threat actor to gain full control of the compromised system. The attackers used Microsoft Word documents as droppers to ensure the Trojan’s stealthy installation. After a malicious document was opened, a macro (Visual Basic script) was run. The macro extracted the malicious program and executed it.
Additional tools were deployed on compromised systems as necessary. These included hard disk monitoring tools, data and password stealers, keyloggers, camera control applications, etc. According to the researchers, the quantity and diversification of tools available in the toolkit indicate a carefully planned attack.
It has not been established to date how the attackers distributed the malicious documents. Most likely, they used phishing emails.
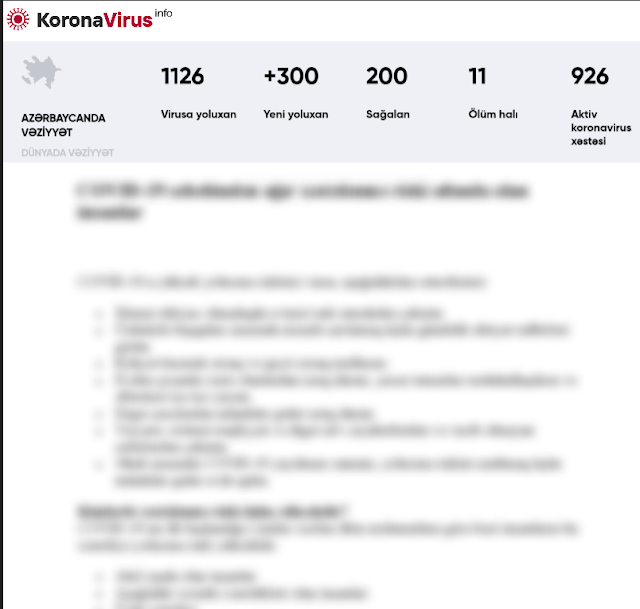
The first attacks were identified in February 2020. They used a malicious document with an image resembling the logo of the Defence R&D Organization of the Indian Ministry of Defence. Two more attack waves were recorded in April. One used bait documents designed to look like the Azerbaijani government’s letters on COVID-19. In the other, the attackers used a file named “C19.docx”. The file, whose name may be a reference to COVID-19, had no readable content.
In addition to the malicious campaigns, the researchers found a phishing site imitating the Azerbaijani government’s web mail, which was designed to steal user credentials.
Source: Cisco Talos
