31 March 2022
Vulnerabilities in Tekon-Automatics solution: (ir)responsible disclosure and scope of the problem
On March 17, an article was released by researcher Jose Bertin in which he described the exploitation of several vulnerabilities in a Tekon-Automatics automation solution. After coming across the publicly available article, we immediately notified the vendor.
First, let’s try to determine the real scope of what happened.
According to a Tekon-Automatics statement (published here), the vulnerable devices are media converters, which have no functionality related to controlling elevator equipment.
The initial entry point into Tekon-Automatics equipment, which can be used to further develop an attack, is default credentials specified in the vendor’s documentation. The researcher refers to this in his article.
The second issue raised by the researcher is privilege escalation, enabling an attacker to achieve the highest (root) privilege level on a system by uploading additional LUA script plugins (CVE-2022-28223). Note that this functionality is actually available on fewer devices than the article states.
We found a total of 141 devices available online. As of the evening of March 25, 58% of available devices had default passwords and only half of these devices had plugin uploading functionality that could be used for privilege escalation.
As of March 29, none of the devices available online used default passwords.
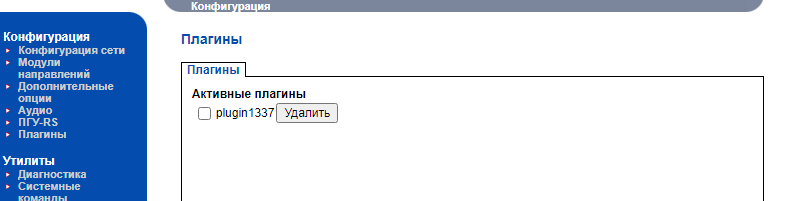
According to our data, not a single malicious attack exploiting this set of vulnerabilities has been identified. We identified a controller on which the researcher apparently tested the privilege escalation vulnerability. As mentioned in the researcher’s article, the plugin uploaded to the device was named “plugin1337”.
Using default passwords is a widespread industrial device configuration error. Running an HTTP server with root privileges is a common architectural problem. Penetration testers and (unfortunately) attackers are happy to take advantage of both these flaws.
The process used to disclose information on the vulnerabilities described raises numerous questions regarding the researcher’s ethics and professionalism.
Vulnerability disclosure should be conducted responsibly. This should involve close collaboration with the vendor and, possibly, with local regulators or a CERT team. This helps lower the chances of threat actors uncontrollably exploiting the vulnerability in question. In this case, the proper approach was not used. The vulnerability information was made publicly available and the researcher didn’t even notify the vendor of the vulnerabilities identified. It is worth noting that this is not the first case of that researcher disclosing vulnerability information irresponsibly: the same person earlier disclosed vulnerabilities in a Chinese vendor’s industrial networking equipment.
In the present situation, using the proper approach to industrial automation system vulnerability disclosure should have top priority. And reaction to such cases of irresponsible behavior should come not only from journalists but also from vendors, computer incident response teams, and local regulators in different countries of the world.
The Tekon-Automatics team has published recommendations on checking network device security settings. It should also be added that defense-in-depth principles should be used at all times and that it is essential to update software and firmware on time, to keep track of the news, and to follow the recommendations provided by regulators.Kaspersky ICS CERT would like to thank the Tekon-Automatics team for their prompt response and their work related to identifying the scope of vulnerability exploitation.
