31 January 2019
Kaspersky Lab has taken part in S4x19 Industrial Cybersecurity Conference
S4x19, one of the largest global industrial cybersecurity conferences in the world, took place on January 14-17, 2019 in South Beach, a neighborhood of Miami Beach, FL. The event brought together leading experts in industrial cybersecurity, including those from Kaspersky Lab, specialists in automated control systems and representatives from vendors such as Schneider Electric, Rockwell Automation, etc. Overall, a total of 536 visitors from all over the world attended the conference.
Conference presentations
World-renowned opinion leaders and cybersecurity experts Dale Peterson, Robert Lee, Colin Parris, and Marty Edwards were just some of the high-profile speakers at the conference.
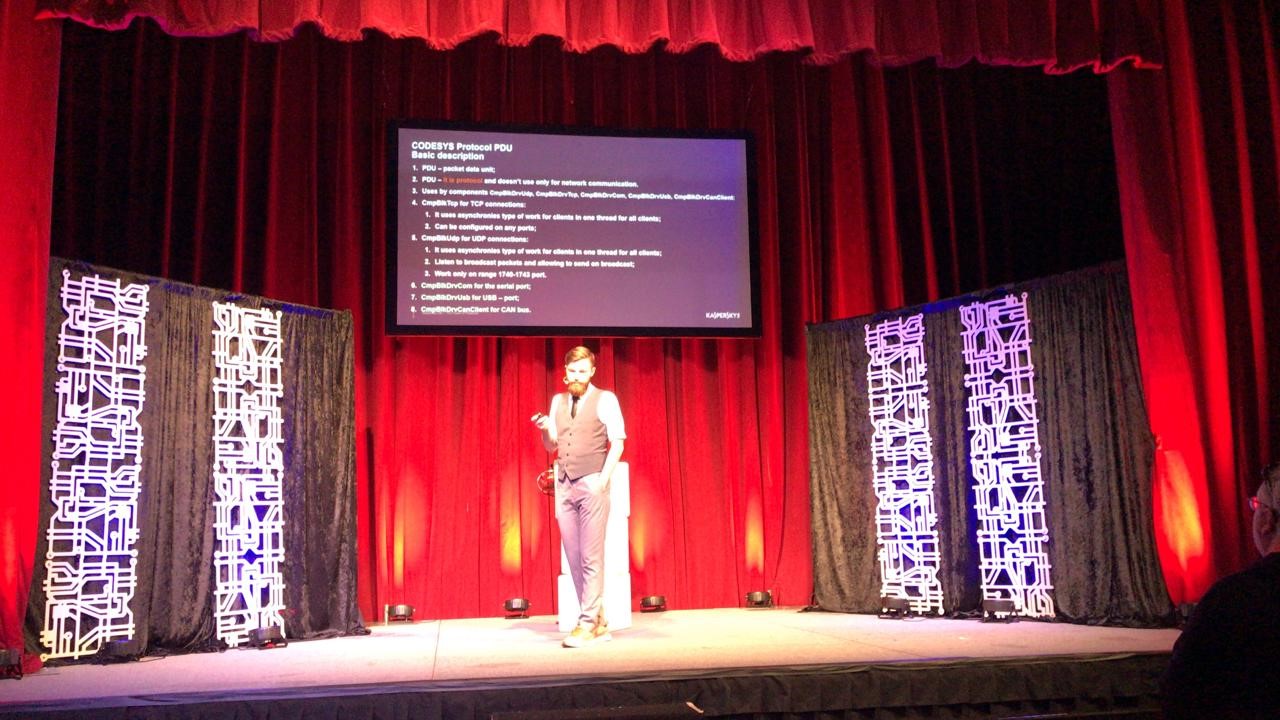
In his presentation, Alexander Nochvay, a security researcher with Kaspersky Lab ICS CERT, focused on vulnerabilities in CoDeSys Runtime, the most popular environment for developing and executing software code for PLCs. CoDeSys Runtime is used globally on more that four million devices made by over 400 companies specializing in industrial automation systems. In his report, Alexander spoke about the fundamental challenges facing information security that stem from the use of OEM products, and demonstrated vulerabilities detected in CoDeSys during research, as well as security problems at the architecture and network protocol implementation levels. A detailed report about these findings will soon be published on the Kaspersky Lab ICS CERT website.
Kaspersky Lab was also represented at the conference’s sponsor session by Vladimir Dashchenko.
ICS Detection Challenge
Besides presentations, the conference organizers also arrange the ICS Detection Challenge to test the wares of industrial security vendors. The contest, held since 2017, brings together various manufacturers of solutions offering information security for technological networks.
Kaspersky Lab and its Kaspersky Industrial Cyber Security (KICS) for Networks solution took part for the first time at this year’s event – one of only two entrants brave enough to take the challenge. The organizers also invited a team of industrial security experts and suggested that they attempt the challenge using only open-source utilities. This offered an opportunity to assess how well commercial solutions from leading information security market players fare against freeware products.
For this year’s ICS Detection Challenge the organizers chose a format that could more accurately be described as a test of digital forensics rather than just attack detection. The participants were challenged to analyze data traffic prepared in advance by the organizers. They had to identify and connect the dots between the 17 steps of a multi-stage attack against a process at a steel plant. For input data, they received 130 GB of network traffic collected in various segments of the office and industrial networks at a real-life facility. The organizers anonymized the traffic and inserted data chunks containing signs of attacks against various parts of the infrastructure. To complicate matters, the organizers added lots of network ‘noise’ to the traffic.
Kaspersky Lab’s team successfully detected the attacks against the industrial network devices using KICS as their detection tool. Afterwards, they gave a video presentation on the conference’s central stage to explain how KICS works.
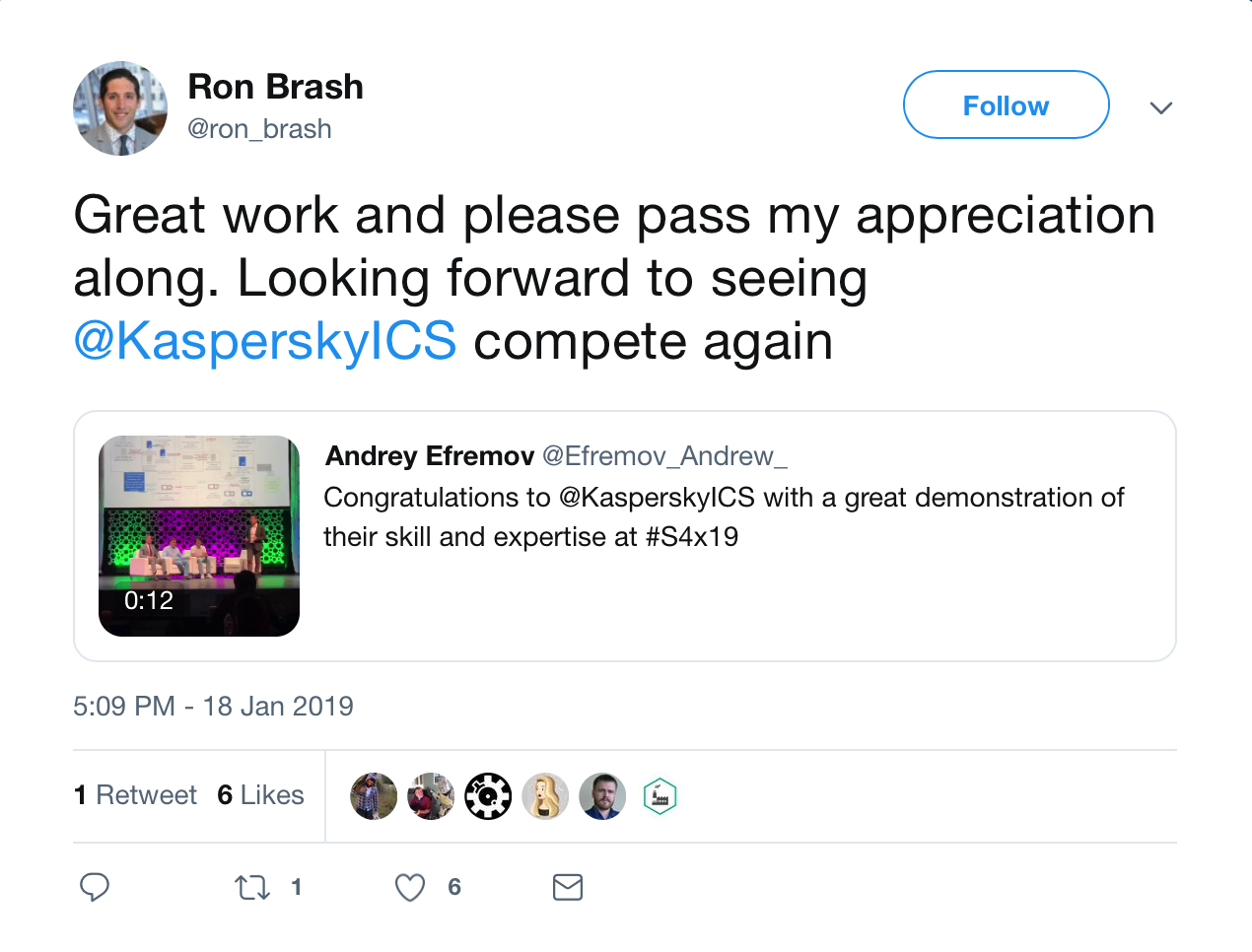
KICS’s performance received positive reviews from the professional community, including Ron Brash of Deloitte, one of the main organizers of the challenge.
The KICS team would like to thank Ron Brash and Dale Peterson for preparing the ICS Detection Challenge and the great opportunity to showcase our product’s operation. That was fun!
See also
-
Detective investigation of APT and rare virus specimens: Kaspersky ICS CERT experts to present new research at KICC
17 September 2025
-
Industrial cybersecurity in 2024: trends and forecasts presented by Evgeny Goncharov, head of Kaspersky’s ICS CERT
26 March 2024
-
TÜV Austria Academy will offer Kaspersky training courses
22 December 2021